Publications
Latest Articles
The Inevitability of Chinese Military Purges
The Third Act of Epic Fury: Why the War of Attrition Against Iran Now Favors America
Featured Book
The New Imperialists: How China, Russia and Iran are trying to remake the world
Today, a new axis of autocrats is trying to reshape the world order and sideline the United States in international affairs.
Latest Policy Paper
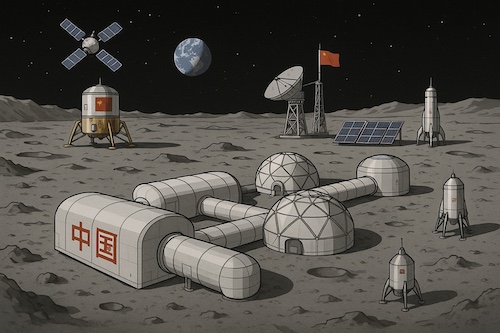
Space Roles and Missions: From Fragmentation to Unity
The United States faces a fundamental organizational crisis in space. America’s space enterprise remains fragmented across multiple agencies with unclear roles, overlapping responsibilities, and competing authorities. This institutional confusion undermines national security, stifles commercial innovation, and threatens U.S. leadership in the vital space domain.
Latest Defense Dossier

Ukraine and the Changing Character of War
Latest In-House Bulletins
Africa Political Monitor No. 62
Nigeria works to mend fences with Washington;
Attack on Niger airport highlights growing extremist threats in Sahel;
Kenya's government accuses Russia of illegal recruitment;
DRC to expand critical mineral supplies to U.S. and UAE;
Sudanese paramilitary training camp identified in Ethiopia
China Policy Monitor No. 1670
China launches fentanyl raids ahead of planned Trump visit;
Executives arrested for smuggling $2.5B in AI chips into China;
Beijing restricts "red-chip" IPOs amid capital flight concerns;
China unlikely to invade Taiwan in 2027, American intelligence says;
Property sector woes continue as prices hit eight-month low
Defense Technology Monitor No. 116
Laser links at sea;
China deploys subsea computing;
The Pentagon is testing cyber defense in orbit...;
...While developing jamming weapons;
The drone-ification of the Black Hawk
Global Islamism Monitor No. 139
Syria's turmoil draws alarm...;
...And regional nations strategize;
...And ISIS regroups in Africa;
Cairo takes fresh aim at the MB
Indo-Pacific Monitor No. 53
China steps toward semiconductor supremacy;
Seoul searching for mineral alliances with Brazil;
Japan to deploy missiles on island near Taiwan;
Pakistan declares open war as cross-border strikes escalate;
Hormuz hinders trade across Asia
Information Warfare Watch No. 53
TikTok disinfo targets Poland;
Euronews faces fresh scrutiny;
Moscow moves to centralize control over nationwide communications;
Turkey moves toward tighter social media rules for minors
Iran Democracy Monitor No. 250
Iraq and the Iran war;
The regime clamps down on Starlink...;
...While platforming its own proponents;
Iran's outsourced intel
Resource Security Watch No. 64
Africa's solar sector surges forward;
A new caucasian trade corridor takes shape;
A mounting Afghan food crisis;
A stockpile to counter China's mineral dominance;
A new role for agriculture in national defense
Russia Policy Monitor No. 2721
Russia's crumbling state;
Russia shares intel with Iran...;
...As Iranian drones head in the other direction;
Network of "disposable agents" conducts sabotage in Europe;
FSB expands elite protection
Ukraine Reform Monitor No. 21
Legislative graft... and an old face;
Kyiv seeks European markets for its defense tech;
...As Kyiv looks beyond China for drone production